The DSS, MageCart, and the DOM – Part 1: The PCI DSS e-Commerce Rules
It turns out that how you implement e-commerce can have a huge impact on your compliance footprint...
2 min read
Neal Christopher : Jun 8, 2016 12:00:00 AM

To accept credit cards in Canada, businesses need to be PCI compliant. Becoming PCI compliant can be difficult in the first place and keeping up with the changes even more so. In April 2016 the Payment Card Industry (PCI) Security Standards Council (formed to regulate security for the payment card industry) released an updated list of compliance requirements known as the PCI Data Security Standard (DSS) v3.2.
Let us guide you through these new requirements. We found thousands of wording changes, most of them innocuous and helpful clarifications, however, a small handful of these changes will require some serious attention in order to maintain compliance after October 2016. The rest of the new requirements are considered best-practice until they become mandatory on February 1, 2018.
Continue reading for everything you need to know about PCI DSS v3.2.
A large number of the new requirements are focused on service providers and these will take significant effort to implement and maintain. Service providers will want to start working towards these new requirements as soon as possible in order to be successful.
Multi-factor authentication is now required for all admin personnel accessing the Cardholder Data Environment (CDE) network or individual systems within the CDE. We see this as the single largest change in v3.2 requiring both merchants and service providers to implement new technical security controls.
E-commerce web redirection servers are back in scope. The PCI SSC announced in their May 2016 assessor newsletter that updates to Self-Assessment Questionnaires SAQ-A, and SAQ-A-EP now have a number of increased requirements to address highly targeted merchant e-commerce web redirection servers. This means e-commerce web redirection servers (using iFrame or Full URL redirection) are back in scope when using SAQ-A eligibility requirements, and third-party web hosts that host these servers are considered third-party service providers under req. 12.8. This redirection scope applies to all entities using either Self-Assessment Questionnaires (SAQ) or Reports on Compliance (ROC) for compliance validation. We anticipate that the related PCI SSC redirection FAQ’s will be updated to clarify this position.
In addition to the thousands of wording changes and 14 numbering changes, there were:
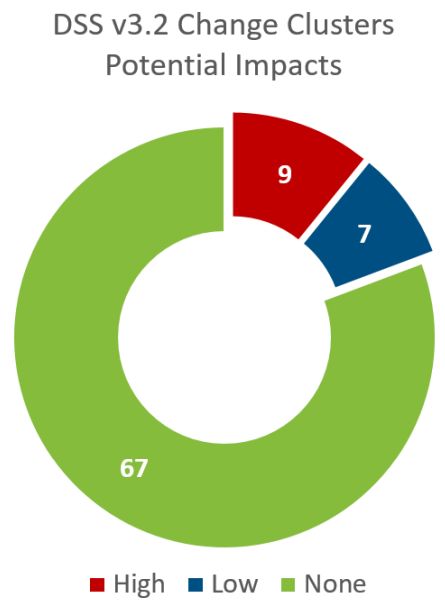
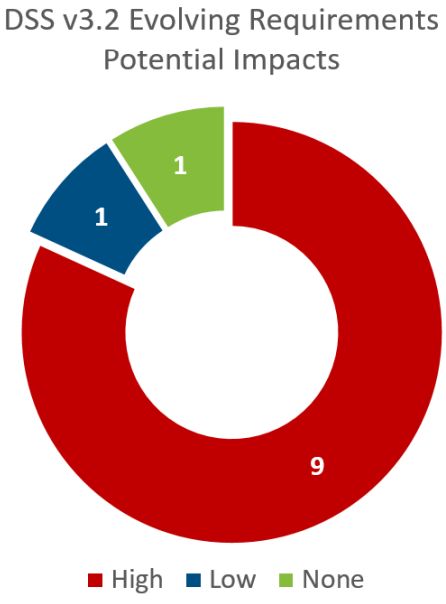
There are several other significant differences between PCI DSS V3.1 and PCI DSS V3.2. To see a quick overview of the rest of the changes, read our Change Analysis Brief. If you would like to know every word that changed, read our Change Analysis Document.

 David Gamey :
Aug 5, 2021 10:07:00 PM
David Gamey :
Aug 5, 2021 10:07:00 PM
It turns out that how you implement e-commerce can have a huge impact on your compliance footprint...

 David Gamey :
Oct 31, 2019 12:00:00 AM
David Gamey :
Oct 31, 2019 12:00:00 AM
If you're subject to PCI DSS you need to understand "The ENTITY". We aren't talking about a...

 David Gamey :
May 15, 2017 10:07:00 PM
David Gamey :
May 15, 2017 10:07:00 PM
On May 1st a critical new and possibly unprecedented vulnerability was announced. The flaw in...